Wrapped BANANO (wBAN) Bridges Rekt — Epilogue
You probably heard about the exploit on wBAN bridges. Shortly after the exploit, a fix was applied and investigations on the identity of the attacker began. Two monkeys were identified: Sqidrod as the attacker and Alibaba as an accomplice who received some stolen funds from the attacker.


You probably heard about the exploit on wBAN bridges.
Shortly after the exploit, a fix was applied and investigations on the identity of the attacker began.
TLDR: Two monkeys were identified: Sqidrod as the attacker and Alibaba as an accomplice who received some stolen funds from the attacker.
Stolen funds have been partially recovered.
The Investigation
With the help of a monkey (running under the alias “octpusstick”) and knowing the BSC/Polygon & BAN wallets of the attacker involved in this attack, multiple pieces of evidence linking Sqidrod (the attacker) and Alibaba (the accomplice) began to emerge.
First of all, because of Sqidrod’s inquiries in Discord, we already suspected him:
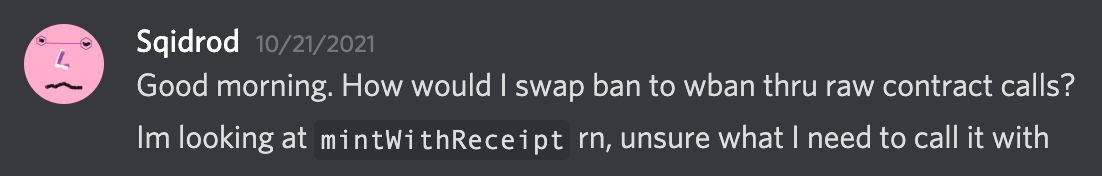
Sqidrod asked about the inner working of mintWithReceipt on Oct 21, and attempted multiple times (example here) to figure it out. They claimed later to be able to bypass the official wBan bridge dApp:
Soon, we knew the addresses of Sqidrod’s Banano wallets and found transactions involving his wallet and one of the Banano wallets used by the attacker.
With further investigation, we were able to find additional evidence linking this attacker to another monkey, and the evidence began to pile up against both Sqidrod and Alibaba.
We contacted Sqidrod and he confessed. Later, we contacted Alibaba who also confessed to receiving some of the stolen funds.
Sqidrod returned some of the stolen funds. Alibaba did not.
Conclusion
Instead of doing the right thing, reporting a bug to help and protect the Banano ecosystem and community, and receiving a BANANO bounty for their efforts, Sqidrod and Alibaba decided to exploit the bug for their own profit. With the help of “octpusstick”, who received a bounty for the help, we were able to recover a portion of the funds. We feel it is important to notify the community that the primary attacker, Sqidrod, is running the bnswap exchange. We are strongly advising to stop using bnswap for your own safety.
Help us improve Banano projects instead of exploiting them!
Call Banonymous tip Hotline at +19 420 66969 for any bug you find, or contact a BRPD near you.

